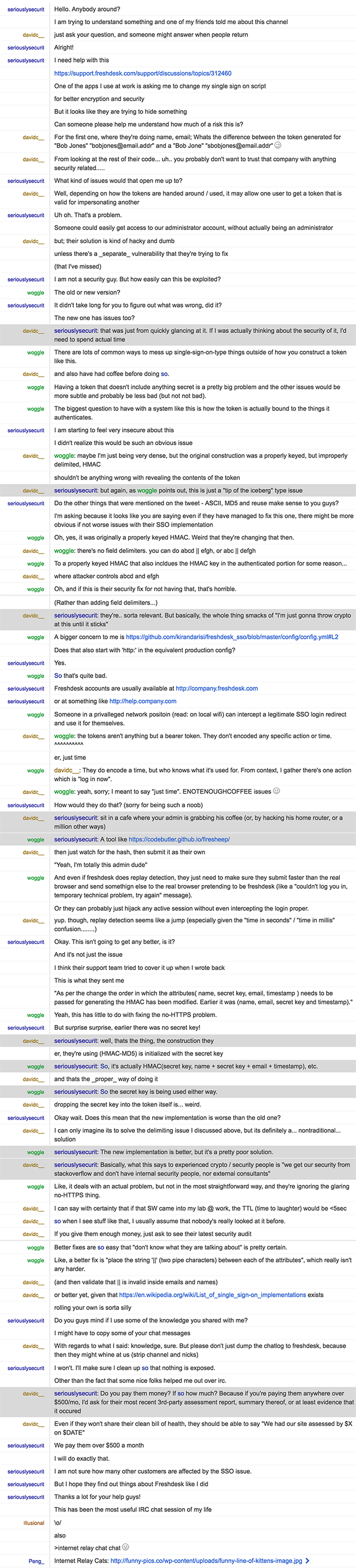
We use Freshdesk at my company for customer support. One of their features that we use, allows us to setup a custom single sign on page for our users, so that they can sign in to the app with their exsting company credentials instead of creating new ones with Freshdesk.
Earlier this week, we received an email from their security team asking us to change our implementation of single sign on for security reasons.
Full first email here: http://pastebin.com/5Lx6nB6y
The email said that I have to do it before Thursday (2 days from receiving the email) which looked like a very short period. I was worried and replied to them asking what was going on and what I needed to do specifically. They told me to change the order of the SSO attributes from (name, email, secret key and timestamp) to (name, secret key, email, timestamp). The earlier method apparently allows a vulnerability and the new one would make single sign on more secure.
Full reply here: http://pastebin.com/Bjgb3ffW
So I went ahead and tried to change our implementation but found that in the script (that Freshdesk gave me), the attributes were in a different order than what they said it was before the change - (name, email, timestamp). The secret key was not included in the code. So I was confused and didn't know what was the next right step. I decided to complain on Twitter about the short notice (like anyone in 2016), but interestingly I found this a tweet from someone about it already.
https://twitter.com/sean_a_cassidy/status/725029900499976193
It led me to two git commits that were made the previous day (the day Freshdesk sent the email)
https://github.com/kirandarisi/freshdesk_sso_java/commit/da813fac3a51c863db8c2abecf95b34489e9b8a4
https://github.com/kirandarisi/freshdesk_sso/commit/9a43c7a0144901d0e33c717d77fba3249b192638
These commits showed that the secret key was added in between the name and email only a day ago and it was the change they wanted us (and presumably others, based on the tweet) to make in our setup. The tweet also talked about other issues related to ASCII, MD5 and Reuse.
So I went back to Freshdesk again to ask them what was going on. Over chat, Affan, the guy who sent me the original reply, refused to acknowledge or tell me why they gave me wrong information the previous day (when they wrongly told me that I just have to change order of the secret key). When I asked to talk to his senior, it didn't really help because even he wouldn't tell me the real implications of the issue if I don't make the change. This chat lasted for more than an hour and it was very painful, but eventually came to nothing. But hey, I made a transcript.
Full chat here: http://pastebin.com/3KDJmfx4
When it finally ended, I decided to find out the impact of the issue by seeking help from others who were affected. I am guessing this is something big because Freshdesk is giving me only two days time to change the script. They also lied to me by saying that I just have to change just the order of the attributes, when clearly, based on the commits, it is something else. I wonder if they downplayed it to me intentionally because they wanted to cover up something bigger.
We are still on the old SSO implementation. And according to the guy on Twitter, it looks like there are more unresolved vulnerabilities. I am posting this anonymously to make sure that someone doesn't use it to get access to our account and data.
Freshdesk isn't ready to give me clear answers. Is there anybody else who is affected by this? Can someone please help me understand what is going on?